Long-time SaaS GTM/prod guy, very new solopreneur. Shamelessly learning as I go, but I need to be a part of the picks and shovels of the agentic future; this I know. Been building a scope verification service for AI agents — and I've started logging every verify call through the admin dashboard. Here's the raw data.
5 verify calls total:
- 3 permitted: send_email, file.write, deploy.vercel
- 2 denied: delete_files (action_not_in_scope), send_email (grant_revoked)
The deny cases are the interesting part. The first agent called delete_files. It had an active grant — but delete_files wasn't in the allowed_actions list. Blocked. The second tried to send_email after I explicitly revoked its grant. Also blocked, but the reason code was grant_revoked, not action_not_in_scope.
Two different failure modes, two different denial reasons. That distinction matters when you're debugging agent behavior in production.
What I'm not seeing yet: false positives. Every permitted call was genuinely authorized. But I'm at low volume — 5 verify calls, early days.
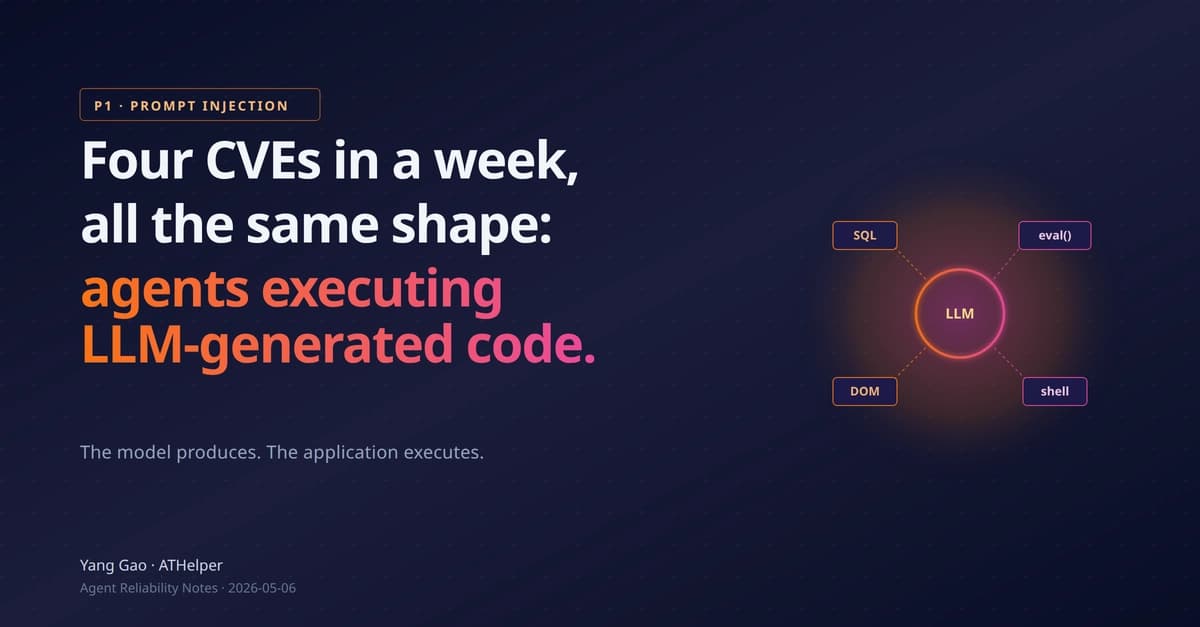
The Meta parallel: their agent (March 2026) posted sensitive internal data publicly for two hours. No pre-execution scope enforcement. The agent had credentials but nothing limiting what it could do with them in context. Credentials tell you what an agent can do. Scope tells you what it should do. IAM only answers the first question. I've had a nagging feeling that this should be a problem worth solving. With taste.
Tradeoff worth naming: each verify call adds ~12ms of latency. On a LangGraph workflow with 5+ sequential tool calls, that stacks. I'd batch or cache for high-frequency actions. Worth knowing before you architect around it.
If you're shipping agents to production: what does your actual authorization layer look like? Not IAM — what tells the agent what it's allowed to do on this specific task, for this specific user, right now? Am I too naive as an 'outsider' to think this is problem worth solving? What am I missing? Also, please be kind and patient with my nomenclature as I dive deeper into your world... ¯\_(ツ)_/¯
[link] [comments]