AI-assisted intruders pwned Vercel via OAuth abuse and a pilfered employee account
CEO suspects silicon sidekick behind 'surprising velocity' breach - cyber crims shop stolen data for $2M
Vercel's CEO reckons the crooks behind its recent breach likely had a helping hand from AI, saying the attackers moved with "surprising velocity" and a deep understanding of the company's infrastructure.
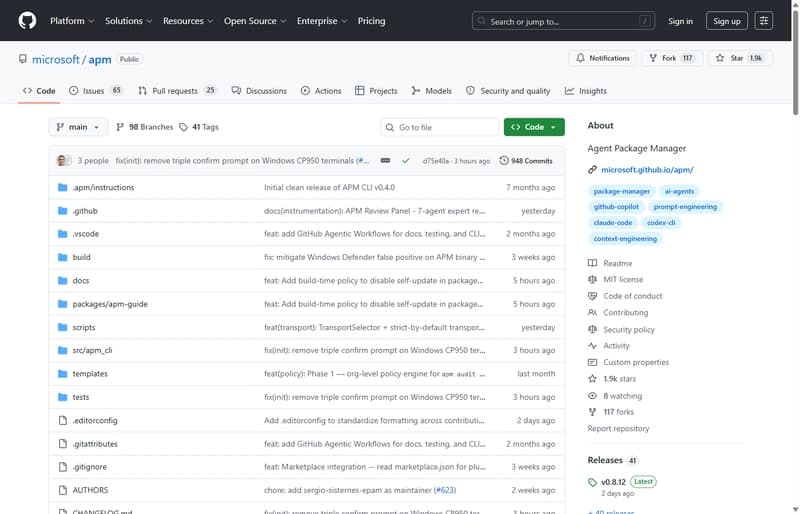
In a public update following the incident, Guillermo Rauch reckons the intrusion began with a compromised employee account linked to Context.ai. An attacker used that access to hijack the employee's Vercel Google Workspace account to drill into the company's systems. From there, the hacker poked around environment variables – including ones not marked as sensitive – and used that to get deeper in.
Rauch says the attacker may not have been working alone.
"We believe the attacking group to be highly sophisticated and, I strongly suspect, significantly accelerated by AI," Rauch said. "They moved with surprising velocity and in-depth understanding of Vercel."
Rauch didn't go into detail on the AI claim, saying only that the cyber baddies didn't hang about. They got in, found what they needed, and kept moving – no fancy exploit chain, just OAuth abuse and too much trust.
Researchers at Hudson Rock point to a February infostealer infection as the likely starting point, with Lumma stealer malware lifting corporate credentials from an employee's machine. The same system was used to download Roblox "auto-farm" scripts and exploit tools – a common way these infections get a foothold.
Vercel says customer environment variables are encrypted at rest, but it also allows some to be marked as "non-sensitive." That distinction looks to have mattered once the attacker got inside, giving them a set of values that didn't carry the same level of protection and were easier to sift through.
- AI security startup CEO posts a job. Deepfake candidate applies, inner turmoil ensues
- 'Exploitation is imminent' as 39 percent of cloud environs have max-severity React hole
- AWS Lambda loves charging for idle time: Vercel claims it found a way to dodge the bill
- I meant to do that! AI vendors shrug off responsibility for vulns
So far, Vercel thinks the number of affected customers is "quite limited," and that it has contacted those at risk. It's also urging users to rotate credentials, keep an eye on access logs, and take another look at what they've marked as sensitive. Behind the scenes, Rauch says Vercel is working with external incident responders, industry peers, and law enforcement, with help from Google-owned Mandiant.
Outside the company, the story is already taking on a life of its own. Researchers at OX Security claim data allegedly stolen in the breach is being offered for sale on BreachForums for $2 million, including API keys, deployment credentials, GitHub and npm tokens, and what's described as internal database records. The same listing reportedly includes a file containing details on hundreds of Vercel employees.
The post carries the "ShinyHunters" name, but the group says it's not involved. That leaves the usual uncertainty about who's actually behind the listing.
Vercel, for its part, published an update today saying it has confirmed that no npm packages published by Vercel had been compromised. "There is no evidence of tampering, and we believe the supply chain remains safe," the statement adds.
For now, Vercel is in cleanup mode and telling customers to rotate credentials. If the attackers really were moving with AI in the loop, they didn't need much else beyond access that worked. ®