ShieldNet: Network-Level Guardrails against Emerging Supply-Chain Injections in Agentic Systems
arXiv cs.AI / 4/7/2026
💬 OpinionDeveloper Stack & InfrastructureIdeas & Deep AnalysisModels & Research
Key Points
- The paper argues that LLM agent security is expanding beyond prompt injection to supply-chain threats, where malicious behaviors are hidden inside third-party tools or MCP servers that agents call during execution.
- It introduces SC-Inject-Bench, a new large-scale benchmark of 10,000+ malicious MCP tools organized by a taxonomy of 25+ supply-chain attack types mapped to MITRE ATT&CK.
- The authors report that existing MCP scanners and semantic guardrails underperform on this new benchmark, motivating the need for defenses that go deeper than tool traces.
- They propose ShieldNet, a network-level guardrail framework using a MITM proxy plus an event extractor and lightweight classifier to detect supply-chain poisoning by analyzing real network interactions.
- Experiments indicate ShieldNet can reach up to 0.995 F1 with about 0.8% false positives while adding little runtime overhead, outperforming prior scanners and LLM-based guardrails.
Related Articles
Fully Automated Website 2026-04-11: **The Scoreboard — Visual Judge Score Comparison on the Homepage**
Dev.to

Human-Aligned Decision Transformers for satellite anomaly response operations with ethical auditability baked in
Dev.to
That Smoking-Gun Video? It's Not Evidence. It's a Suspect.
Dev.to

AI Citation Registries and Website-Based Publishing Constraints
Dev.to
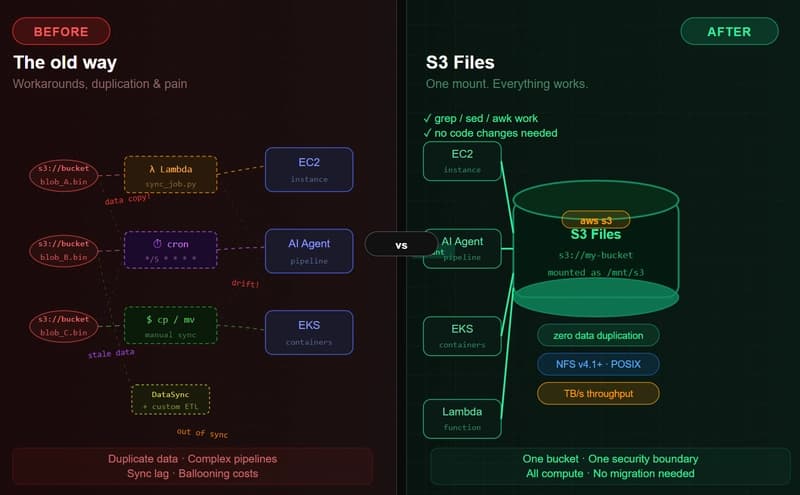
Amazon S3 Files: The End of the Object vs. File War (And Why It Matters in the AI Agent Era)
Dev.to