INTARG: Informed Real-Time Adversarial Attack Generation for Time-Series Regression
arXiv cs.LG / 4/15/2026
📰 NewsSignals & Early TrendsIdeas & Deep AnalysisModels & Research
Key Points
- The paper addresses the vulnerability of deep learning time-series forecasting models to adversarial attacks and notes that many existing attack methods do not fit realistic time-series constraints.
- It introduces INTARG, an online bounded-buffer adversarial attack framework designed for time-series regression without needing full historical storage or attacking at every time step.
- INTARG uses an informed and selective strategy that targets only certain time steps—specifically where the model is highly confident and where expected prediction error is maximal.
- Experiments reported in the paper show up to a 2.42x increase in prediction error while executing attacks in fewer than 10% of time steps, indicating higher attack efficiency.
- Overall, the work contributes a more practical adversarial attack methodology for time-series forecasting under online, resource-limited settings.
Related Articles

Black Hat Asia
AI Business

The Complete Guide to Better Meeting Productivity with AI Note-Taking
Dev.to

5 Ways Real-Time AI Can Boost Your Sales Call Performance
Dev.to
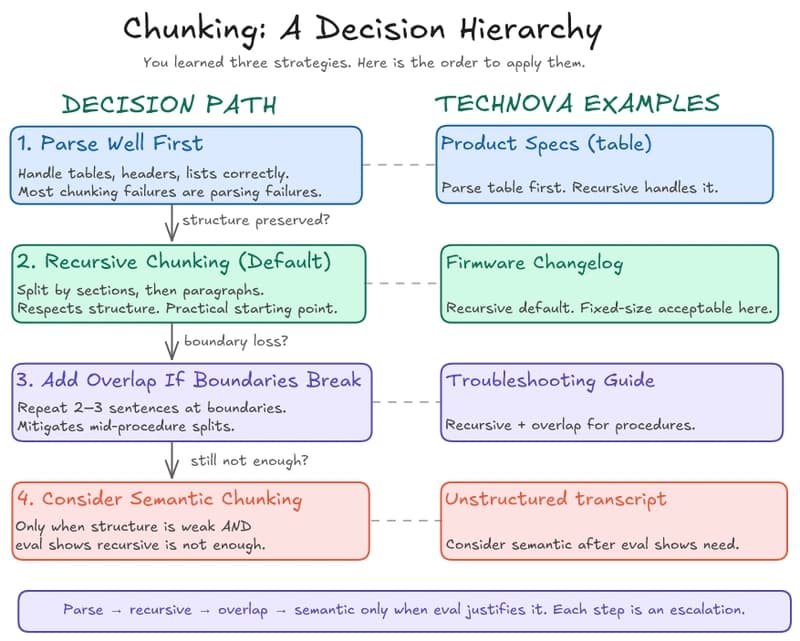
RAG in Practice — Part 4: Chunking, Retrieval, and the Decisions That Break RAG
Dev.to
Why dynamically routing multi-timescale advantages in PPO causes policy collapse (and a simple decoupled fix) [R]
Reddit r/MachineLearning