A Public Theory of Distillation Resistance via Constraint-Coupled Reasoning Architectures
arXiv cs.AI / 3/27/2026
💬 OpinionSignals & Early TrendsIdeas & Deep AnalysisModels & Research
Key Points
- The paper argues that the key risk in knowledge distillation and model extraction is not just copying behavior, but transferring capability more cheaply than the governance controls that originally protected it.
- It proposes a “constraint-coupled reasoning” architectural thesis in which distillation becomes a weaker shortcut when high-level capability is tied to internal stability constraints governing state transitions over time.
- The framework formalizes four components—bounded transition burden, path-load accumulation, dynamically evolving feasible regions, and a capability–stability coupling condition—to define and analyze the threat model.
- The work is designed to be trade-secret-safe and intentionally avoids proprietary implementation details, training recipes, instrumentation, deployment procedures, and confidential system design choices.
- It is presented as theoretical but falsifiable, with experimentally testable hypotheses aimed at future research on distillation resistance, alignment, and model governance.
広告
Related Articles
Got My 39-Agent System Audited Live. Here's What the Maturity Scorecard Revealed.
Dev.to
The Redline Economy
Dev.to
$500 GPU outperforms Claude Sonnet on coding benchmarks
Dev.to
From Scattershot to Sniper: AI for Hyper-Personalized Media Lists
Dev.to
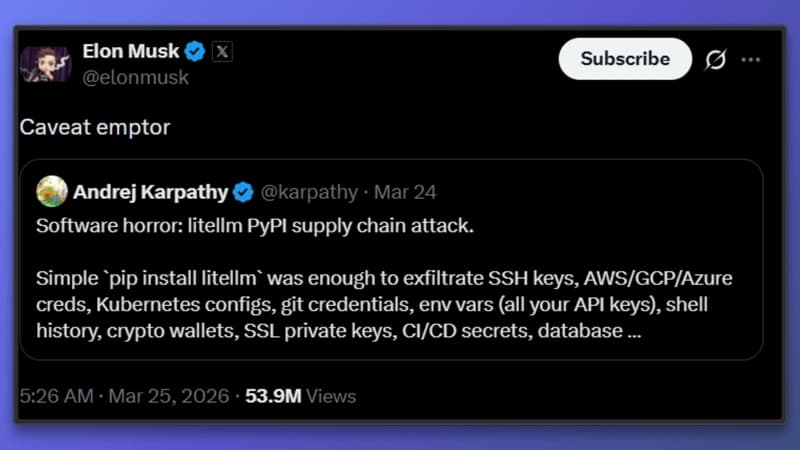
The LiteLLM Supply Chain Attack: A Wake-Up Call for AI Infrastructure
Dev.to