Skills as Verifiable Artifacts: A Trust Schema and a Biconditional Correctness Criterion for Human-in-the-Loop Agent Runtimes
arXiv cs.AI / 5/4/2026
💬 OpinionDeveloper Stack & InfrastructureIdeas & Deep AnalysisModels & Research
Key Points
- The paper argues that “agent skills” (structured instruction/script/reference bundles used with an LLM) should be treated as untrusted code until explicitly verified by the runtime that loads them.
- It emphasizes that relying on trust signals like signatures, clearance levels, or registry provenance is unsafe, and instead the runtime must enforce a default-deny posture until verification passes.
- Without skill verification, human-in-the-loop (HITL) oversight must run on every irreversible action, which the authors say becomes impractical and turns into ineffective rubber-stamping at scale.
- The authors propose a trust schema with per-skill manifest verification levels, a capability gate whose HITL policy depends on those levels, and a “biconditional” correctness criterion that any verification method must satisfy under adversarial evaluation.
- They also provide a portable runtime profile with ten normative guidelines derived from a working open-source reference implementation, aiming for model-agnostic adoption without retraining or fine-tuning.
💡 Insights using this article
This article is featured in our daily AI news digest — key takeaways and action items at a glance.
Related Articles
A very basic litmus test for LLMs "ok give me a python program that reads my c: and put names and folders in a sorted list from biggest to small"
Reddit r/LocalLLaMA
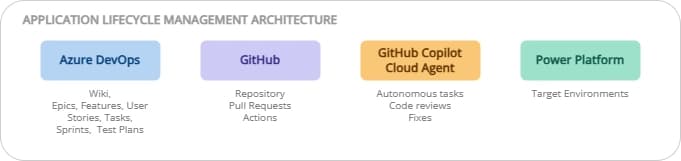
ALM on Power Platform: ADO + GitHub, the best of both worlds
Dev.to

Iron Will, Iron Problems: Kiwi-chan's Mining Misadventures! 🥝⛏️
Dev.to
Experiment: Does repeated usage influence ChatGPT 5.4 outputs in a RAG-like setup?
Dev.to
Find 12 high-volume, low-competition GEO content topics Topify.ai should rank on
Dev.to