Compatibility at a Cost: Systematic Discovery and Exploitation of MCP Clause-Compliance Vulnerabilities
arXiv cs.AI / 3/12/2026
💬 OpinionIdeas & Deep Analysis
Key Points
- The paper identifies a new attack surface called compatibility-abusing attacks that arise from the MCP's optional clauses, enabling risks such as silent prompt injection and DoS across multi-language SDKs.
- It presents a universal intermediate representation (IR) generator to normalize MCP SDKs across languages, enabling cross-language analysis of compliance.
- It proposes an auditable static analysis workflow guided by large language models to reason about cross-language and cross-clause compliance in MCP implementations.
- It formalizes the attack semantics of MCP clauses and builds a three-modality pipeline to uncover exploitable non-compliance issues.
広告
Related Articles
Got My 39-Agent System Audited Live. Here's What the Maturity Scorecard Revealed.
Dev.to
The Redline Economy
Dev.to
From Scattershot to Sniper: AI for Hyper-Personalized Media Lists
Dev.to
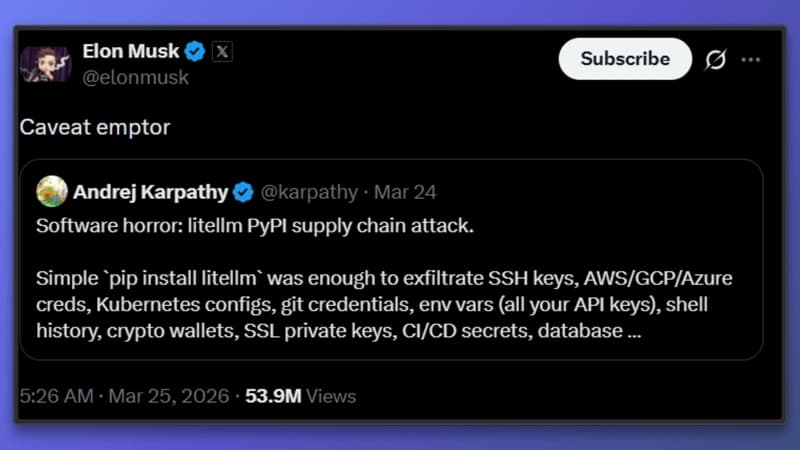
The LiteLLM Supply Chain Attack: A Wake-Up Call for AI Infrastructure
Dev.to
[D] Real-time Student Attention Detection: ResNet vs Facial Landmarks - Which approach for resource-constrained deployment?
Reddit r/MachineLearning