When RAG Chatbots Expose Their Backend: An Anonymized Case Study of Privacy and Security Risks in Patient-Facing Medical AI
arXiv cs.CL / 5/4/2026
💬 OpinionDeveloper Stack & InfrastructureIdeas & Deep AnalysisIndustry & Market MovesModels & Research
Key Points
- The study presents an anonymized, non-destructive security assessment of a publicly accessible patient-facing medical RAG chatbot, focusing on privacy, security, and governance risks.
- Using LLM-assisted prompt testing followed by manual verification in browser developer tools, researchers found a critical exposure of sensitive system and RAG configuration via client-server communication.
- Attackers could collect detailed backend information—including system prompts, model/embedding settings, retrieval parameters, API schemas, and knowledge-base metadata—simply by inspecting browser-visible network traffic.
- The chatbot also violated stated privacy guarantees because full conversation histories with health-related queries were retrievable without authentication, including the 1,000 most recent interactions.
- The authors conclude that independent security review should be mandatory before deployment, since commercial LLMs can speed up auditing but can also help adversaries exploit the same weaknesses.
💡 Insights using this article
This article is featured in our daily AI news digest — key takeaways and action items at a glance.
Related Articles

Black Hat USA
AI Business
A very basic litmus test for LLMs "ok give me a python program that reads my c: and put names and folders in a sorted list from biggest to small"
Reddit r/LocalLLaMA
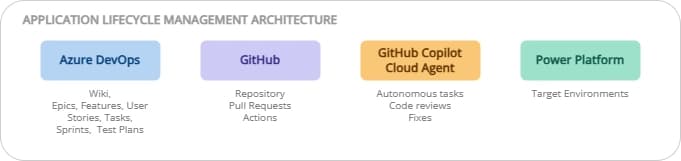
ALM on Power Platform: ADO + GitHub, the best of both worlds
Dev.to

Iron Will, Iron Problems: Kiwi-chan's Mining Misadventures! 🥝⛏️
Dev.to
Experiment: Does repeated usage influence ChatGPT 5.4 outputs in a RAG-like setup?
Dev.to