Learning From Developers: Towards Reliable Patch Validation at Scale for Linux
arXiv cs.AI / 3/27/2026
💬 OpinionIdeas & Deep AnalysisTools & Practical UsageModels & Research
Key Points
- The paper analyzes a decade of Linux memory-management patch reviews, finding that human effort still dominates despite many automated checking tools and that review capacity is bottlenecked by a small number of maintainers.
- It proposes FLINT, a patch validation framework that combines rule-based analysis derived from historical developer discussions with an LLM that avoids training or fine-tuning on new data.
- FLINT uses a multi-stage method to extract the most relevant context from past discussions, then retrieves matching validation rules for new patches and produces reference-backed reports for easier developer interpretation.
- The system targets defects that traditional tools often miss, including maintainability problems (e.g., design choices and naming) and hard concurrency bugs (e.g., deadlocks and data races).
- Reported results indicate FLINT found new issues in the Linux v6.18 cycle, improved higher-ground-truth coverage on concurrency bugs versus an LLM-only baseline, and reduced false positives.
広告
Related Articles
![[Boost]](/_next/image?url=https%3A%2F%2Fmedia2.dev.to%2Fdynamic%2Fimage%2Fwidth%3D800%252Cheight%3D%252Cfit%3Dscale-down%252Cgravity%3Dauto%252Cformat%3Dauto%2Fhttps%253A%252F%252Fdev-to-uploads.s3.amazonaws.com%252Fuploads%252Fuser%252Fprofile_image%252F3618325%252F470cf6d0-e54c-4ddf-8d83-e3db9f829f2b.jpg&w=3840&q=75)
[Boost]
Dev.to

Managing LLM context in a real application
Dev.to

Got My 39-Agent System Audited Live. Here's What the Maturity Scorecard Revealed.
Dev.to

OpenAI Killed Sora — Here's Your 10-Minute Migration Guide (Free API)
Dev.to
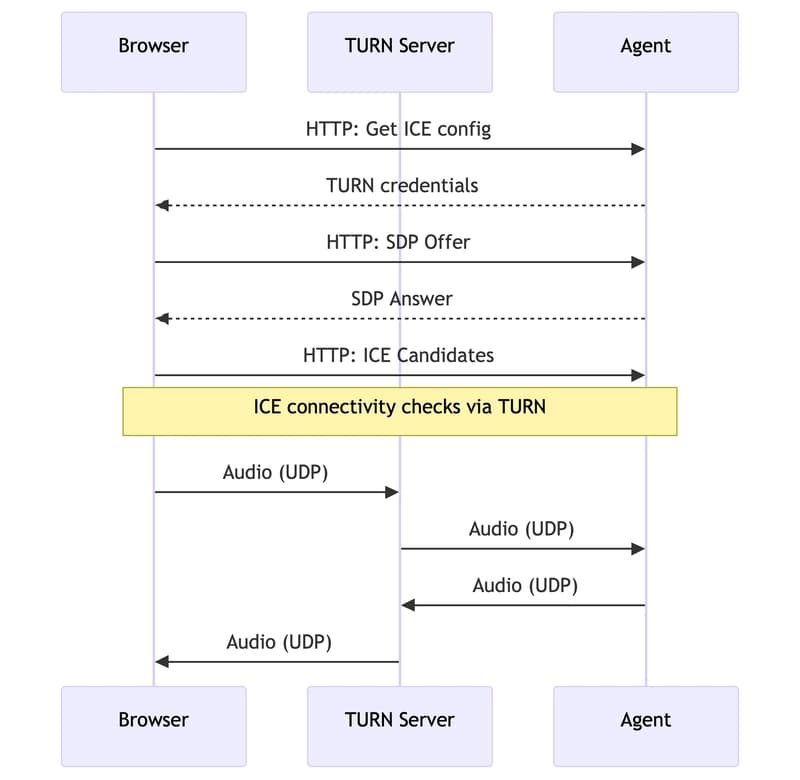
Switching my AI voice agent from WebSocket to WebRTC — what broke and what I learned
Dev.to