 | Built an eBPF-based tracer that captures LLM API and MCP traffic from any process on your machine — no SDK changes, no proxy, no code instrumentation. It intercepts TLS via OpenSSL uprobes and parses Anthropic, OpenAI, and Gemini API calls in real time. Extracts model, tokens, latency, TTFT, tool names, streaming status, and full request/response bodies. Also traces MCP calls over stdio/socketpairs and HTTP (so Claude Code tool use shows up too). Outputs JSONL, exports to OpenTelemetry and Prometheus. Linux only, needs root for eBPF probes. Works with Python, Node.js, and anything using OpenSSL with exported symbols. Doesn't work with Go, Bun, Deno, or rustls. GitHub: https://github.com/zhebrak/agtap [link] [comments] |
Trace your LLM API and MCP calls with zero code changes (eBPF, Linux)
Reddit r/LocalLLaMA / 3/12/2026
📰 NewsDeveloper Stack & InfrastructureTools & Practical Usage
Key Points
- An eBPF-based tracer is introduced that can capture LLM API and MCP traffic from any process on a Linux machine without SDK changes, proxies, or code instrumentation.
- It intercepts TLS via OpenSSL uprobes and can parse calls to Anthropic, OpenAI, and Gemini in real time, extracting model, tokens, latency, TTFT, tool names, streaming status, and full request/response bodies.
- It also traces MCP calls over stdio/socketpairs and HTTP, so uses of Claude Code tool appear in traces as well; outputs JSONL and can export to OpenTelemetry and Prometheus.
- The tool is Linux-only, requires root for eBPF probes, and works with Python, Node.js, and any app using OpenSSL with exported symbols, but not with Go, Bun, Deno, or rustls.
- GitHub repository: https://github.com/zhebrak/agtap
Related Articles
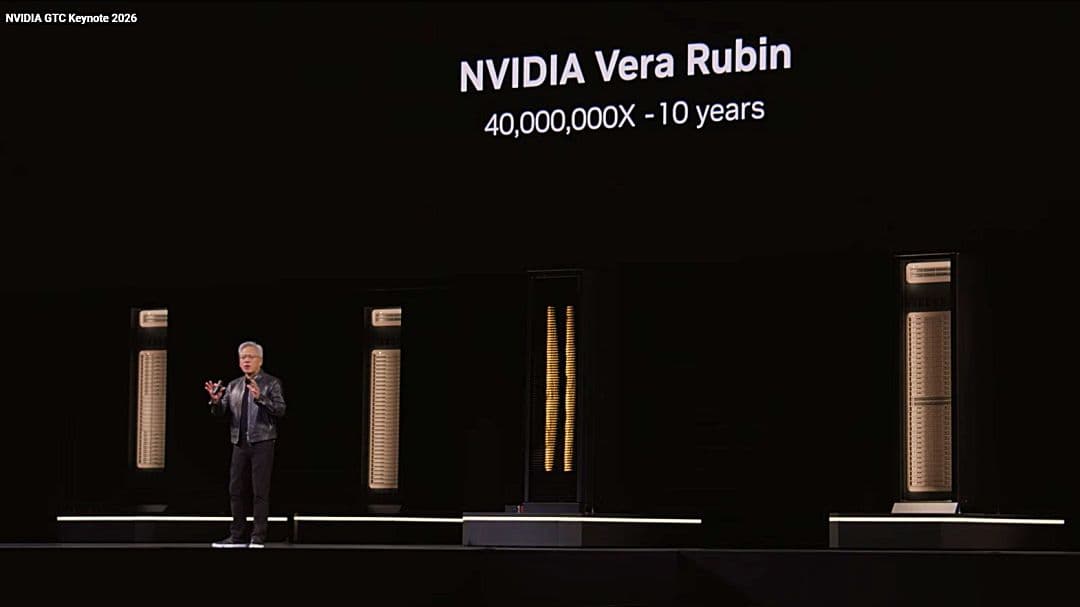
NVIDIA、GTC 2026で次世代AI基盤を発表 「Vera Rubin」を軸にエージェント・ゲーム・宇宙領域へ展開のサムネイル画像
Ledge.ai

1Password、AIエージェントのアクセス制御を統合管理する「Unified Access」発表 人間・マシン・AIの資格情報を一元統制のサムネイル画像
Ledge.ai

『モンドーモンドー』|夏目龍頭流闇文学|AI画像生成|自由詩|散文詩|ホラー|ダークファンタジー|深淵図書館
note

「お金、見直したいけどどこから?」AIが改善ヒントを教えてくれる、公式プロンプトを公開
note

Copilotと物語を作ってみた #213 めーっちゃボロボロこぼす女の子の物語
note