SUDP: Secret-Use Delegation Protocol for Agentic Systems
arXiv cs.AI / 4/29/2026
💬 OpinionDeveloper Stack & InfrastructureIdeas & Deep AnalysisModels & Research
Key Points
- The paper identifies a core security risk in agentic systems that use user secrets: bearer-secret interfaces can turn prompt injection or tool compromise into durable account compromise by exposing reusable authority.
- It formalizes the “Agent Secret Use (ASU)” problem and provides a security taxonomy that distinguishes the structural requirements of safe secret-backed operations from robustness conditions needed in concrete designs.
- The authors propose the Secret-Use Delegation Protocol (SUDP), a three-role protocol in which a requester proposes an operation, the user issues a fresh authenticator-backed single-use grant, and a custodian redeems it to perform bounded use without reusable authority crossing back to the requester.
- They specialize SUDP for agentic deployments where agents propose operations but never directly retrieve secrets, and they argue—under explicit assumptions—that SUDP achieves verifiable authorization, operation-boundedness, and single-use properties.
- The protocol is also analyzed for additional security goals such as storage confidentiality, key isolation across wrapping epochs, and plaintext-level forward secrecy that depends on secret rotation and revocation by the environment.
Related Articles
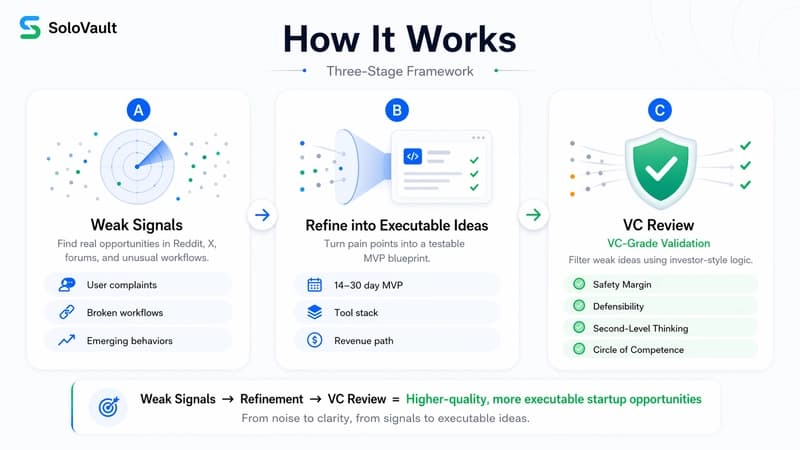
What to Build Still Beats How
Dev.to

I Build Systems, Flip Land, and Drop Trap Music — Meet Tyler Moncrieff aka Father Dust
Dev.to
From Claim Denials to Smart Decisions: My Experience Using AI in Healthcare Claims Processing
Dev.to
Whatsapp AI booking system in one prompt in 5 minutes
Dev.to
v0.22.1
Ollama Releases