When LoRA Betrays: Backdooring Text-to-Image Models by Masquerading as Benign Adapters
arXiv cs.CV / 4/27/2026
💬 OpinionSignals & Early TrendsModels & Research
Key Points
- The paper introduces “Masquerade-LoRA (MasqLoRA),” a systematic attack method that uses a standalone LoRA adapter to stealthily backdoor text-to-image diffusion models.
- By keeping the base model frozen and training only low-rank adapter weights with a small set of trigger word–target image pairs, the attacker creates a malicious adapter that is behaviorally indistinguishable from a benign LoRA until activated.
- The backdoor works via a hidden cross-modal mapping: when a specific text trigger and the malicious LoRA are used, the model outputs a predefined visual result.
- Experiments show the attack can be trained with minimal overhead and reaches a very high attack success rate of 99.8%, indicating a serious risk for the LoRA-heavy open sharing ecosystem.
- The authors argue the AI supply chain needs urgent, dedicated defenses tailored to modular adapter-based workflows like LoRA sharing.
💡 Insights using this article
This article is featured in our daily AI news digest — key takeaways and action items at a glance.
Related Articles
Subagents: The Building Block of Agentic AI
Dev.to
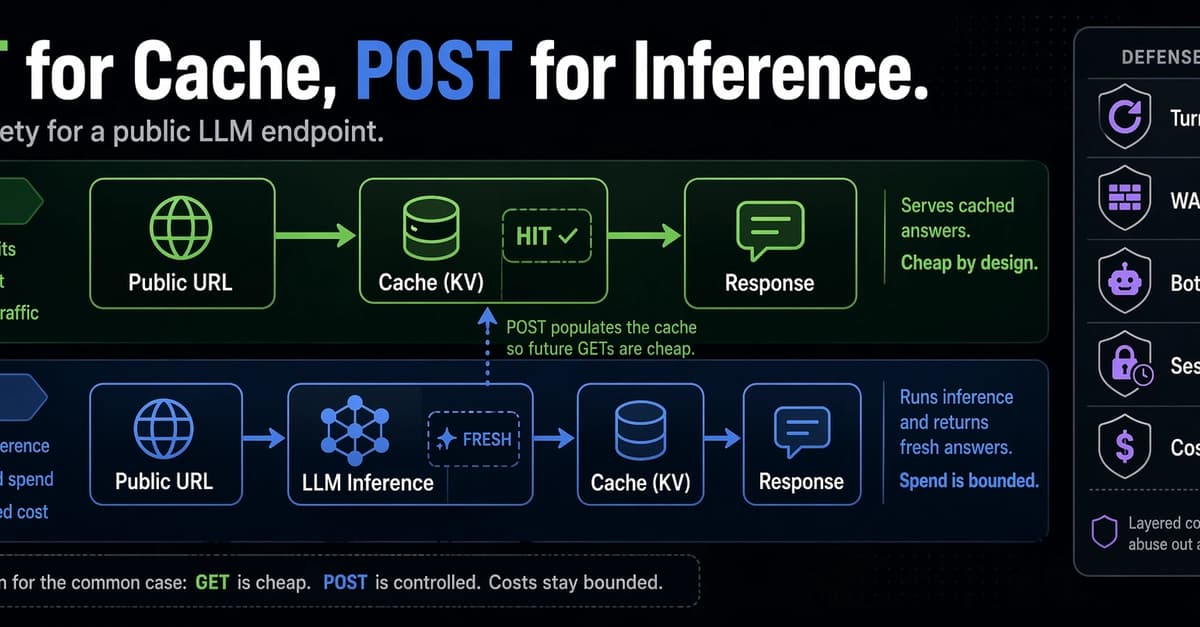
GET Serves Cache, POST Runs Inference: Cost Safety for a Public LLM Endpoint
Dev.to

DeepSeek-V4 Models Could Change Global AI Race
AI Business

Got OpenAI's privacy filter model running on-device via ExecuTorch
Reddit r/LocalLLaMA

The Agent-Skill Illusion: Why Prompt-Based Control Fails in Multi-Agent Business Consulting Systems
Dev.to